Your cart is empty.

What are the 3 Types of Access Control?
Unlocking Building Security: What are the 3 Types of Access Control?

In the realm of building security, safeguarding access to physical spaces is of paramount importance. As technology continues to evolve, so do the methods used to control and regulate entry into buildings. But, what are the 3 types of access control?
In this article, we will delve into the world of access control and explore the three fundamental types that play a pivotal role in enhancing the safety of businesses. Whether you’re managing an office complex, educational institution, or any other facility, understanding these access control methods – Discretionary Access Control (DAC), Role-Based Access Control (RBAC), and Attribute-Based Access Control (ABAC) – will empower you to make informed decisions regarding your building’s security infrastructure.
Monarch, a trusted seller of Verkada products, is here to guide you through the nuances of these access control systems and help you create a secure environment for your occupants.
What are the 3 Types of Access Control: Discretionary Access Control

What are the 3 types of access control? The first is Discretionary Access Control (DAC), which stands as a foundational method in the realm of building security. It offers a vital layer of protection by granting individuals varying levels of access based on their identity. This method places the decision-making authority in the hands of the administrator, who determines who is allowed to enter specific areas.
Characterized by its flexibility and simplicity, DAC enables organizations to assign different access rights to different individuals, depending on their roles and responsibilities. This ensures that only authorized personnel gain entry to sensitive areas, preventing unauthorized access and reducing the risk of security breaches.
Use cases for physical DAC are extensive and include applications such as controlling access to restricted zones within office buildings, laboratories, and server rooms. By leveraging the power of Monarch’s Verkada products, businesses can implement and manage physical DAC effectively, enhancing their building’s security infrastructure.
What are the 3 Types of Access Control: Role-Based Access Control

The second type of access control, Role-Based Access Control (RBAC), is a sophisticated approach to security management that assigns permissions based on an individual’s defined role within an organization. In this model, access is granted not to individuals directly, but to predefined roles, ensuring that employees are granted the appropriate level of access based on their responsibilities.
The key components of RBAC include roles, permissions, and a hierarchical structure. Roles represent job functions, permissions dictate what actions each role can perform, and the hierarchical structure helps in organizing roles in a logical manner. This approach streamlines security management, reduces the risk of unauthorized access, and simplifies the process of granting or revoking access when roles change.
Use cases for physical RBAC include educational institutions, where students, teachers, and administrators have varying levels of access to different parts of the campus. Monarch, with its Verkada products, help businesses ensure building security without compromising operational efficiency.
What are the 3 Types of Access Control: Attribute-Based Access Control

The third and final type of access control, Attribute-Based Access Control (ABAC), is a dynamic and flexible approach to managing access in physical security systems. In this model, access decisions are based on attributes associated with users, resources, and environmental conditions. Attributes can include factors like an individual’s role, location, time, and even device characteristics. ABAC evaluates these attributes to determine whether access should be granted or denied.
Key elements of ABAC include policies that define access rules, attributes that provide contextual information, and a policy enforcement point that evaluates access requests. ABAC’s strength lies in its ability to tailor access based on specific criteria, allowing for fine-grained control. Use cases for ABAC in physical security include large office buildings where employees, contractors, and visitors have varying levels of access based on their roles, schedules, and locations.
Comparing Access Control Methods: Choosing the Right Approach for Your Security Needs

Now that we have answered the question, “what are the 3 types of access control”, we can compare these 3 types. When it comes to enhancing security for physical spaces, understanding the differences between Discretionary Access Control (DAC), Role-Based Access Control (RBAC), and Attribute-Based Access Control (ABAC) is crucial.
DAC provides a basic level of control by allowing users to manage their own resource access. RBAC introduces a structured hierarchy by assigning roles to users and controlling permissions based on those roles. ABAC takes a more dynamic approach, granting access based on various attributes.
To decide which method is best, factors like security needs, organizational structure, and complexity should be considered. DAC may suit smaller organizations, while RBAC offers scalability and efficiency for larger ones. ABAC is ideal for environments with intricate access requirements. Monarch, offering Verkada products, helps tailor the right access control solution for every unique security scenario.
An Overview of Verkada’s Door Access Control Systems for Businesses
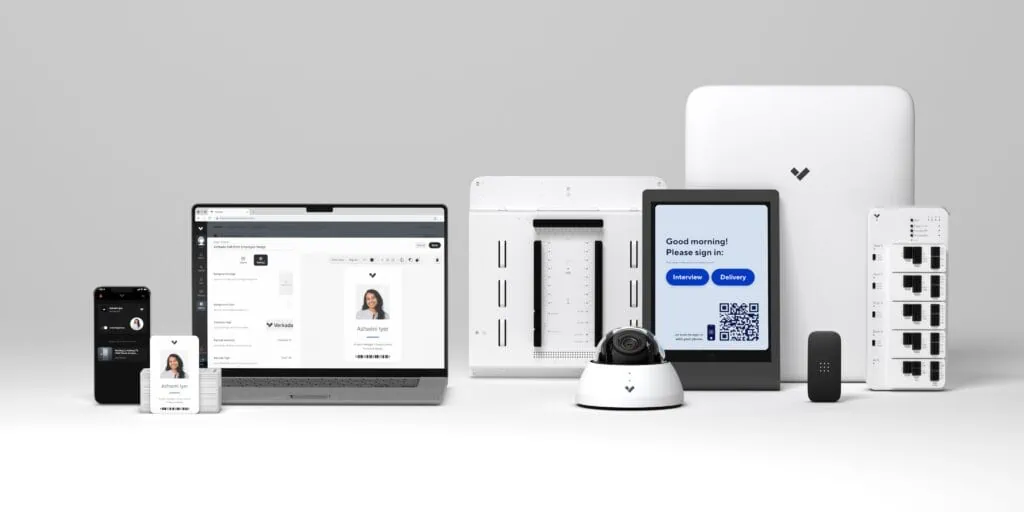
Monarch offers Verkada’s access control systems for businesses. Consider the key features that make Verkada’s systems stand out:
- Centralized Management: Access and manage your access control system from anywhere with a cloud-based platform that is easy-to-use, simplifying administration and oversight.
- Customizable Access Levels and Schedules: Role-based and attribute-based access control. Allows for tailored access control based on employee roles and schedules.
- Real-Time Alerts: Receive SMS and email alerts for doors held open, suspicious entry, and emergency scenarios, allowing for immediate response and threat mitigation.
- Mobile Access: Enjoy the convenience of mobile credentials, enabling authorized individuals to access secured areas using their smartphones.
- Touchless Solutions: Embrace touchless access options, reducing physical contact and addressing hygiene concerns.
- Visitor Management Integration: Efficiently manage visitor access and streamline registration processes by integrating visitor management functionalities.
- Robust Security: Benefit from robust security measures, including encryption, multi-factor authentication, and audit trails, to protect your premises.
How it Works
You can manage your access control system on the Verkada Command platform which is where you can monitor all of your devices.
- Specify the user groups or access levels of the facility on Verkada Command.
- Design badge templates for each user group or access level
- Print the badges and issue credentials either in bulk or individually
Experience the future of access control technologies with Monarch.
Conclusion: What are the 3 Types of Access Control?

In the realm of physical access control, understanding the three main types—Discretionary Access Control (DAC), Role-Based Access Control (RBAC), and Attribute-Based Access Control (ABAC)—is essential to designing a robust security strategy. Each method brings its unique strengths, catering to various security needs and organizational structures.
While DAC grants simplicity and user autonomy, RBAC provides structure and scalability for larger setups. ABAC, with its dynamic attribute-based approach, suits complex environments. As security becomes increasingly vital, Monarch, a trusted vendor of Verkada products, stands ready to assist in tailoring the optimal access control solution.
With the knowledge of these access control methods, organizations can confidently safeguard their premises, assets, and personnel.
Updated: Aug 16













 Jon Jones
Jon Jones


 Courtney Durler
Courtney Durler